Unlocking the Future of Cybersecurity: A Deep Dive into CUSM SDN 2025
Unlocking the Future of Cybersecurity: A Deep Dive into CUSM SDN 2025
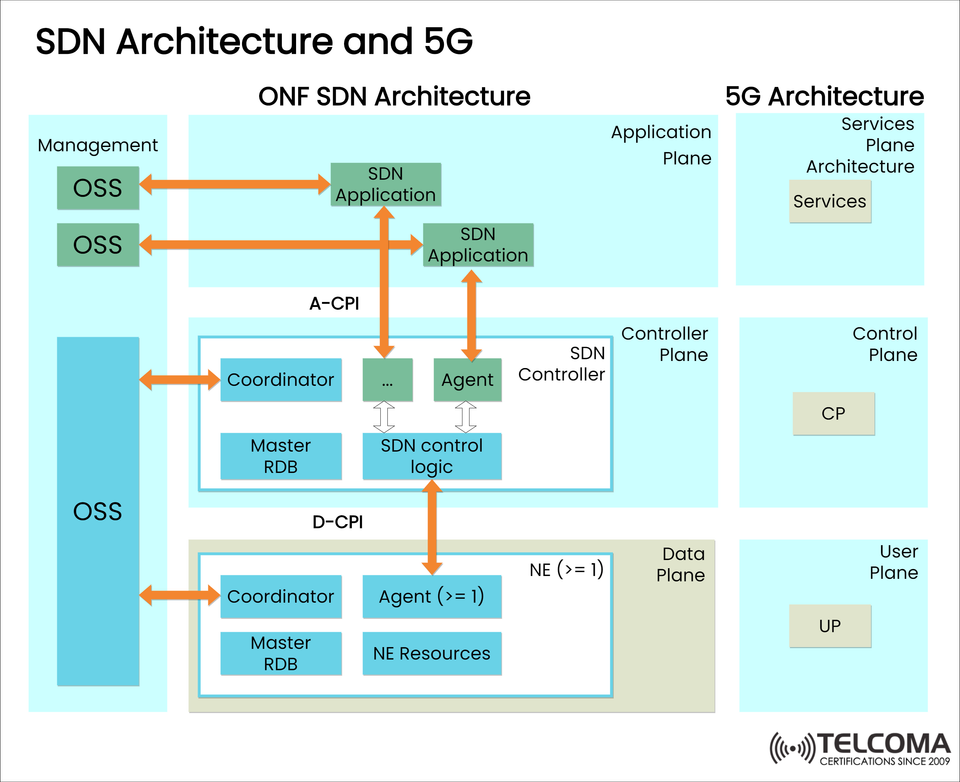
The world of cybersecurity is rapidly evolving, with new threats and vulnerabilities emerging daily. To combat these challenges, organizations are turning to innovative solutions like Carrier-Grade Unified Security Management (CUSM) Software-Defined Networking (SDN) 2025. This cutting-edge technology promises to revolutionize the way we approach network security, providing a robust and scalable framework for protecting against even the most sophisticated attacks. In this article, we'll explore the key features and benefits of CUSM SDN 2025, and examine its potential to shape the future of cybersecurity.
CUSM SDN 2025 is a comprehensive security framework that leverages advanced network programmability and analytics to provide real-time threat detection and response. By integrating security functions across the network, CUSM SDN 2025 enables administrators to monitor and control network traffic with unprecedented precision, identifying potential security breaches before they occur. This approach not only improves overall network security but also enhances the efficiency and reliability of network operations.
According to industry expert, Dr. Rachel Kim, Director of Cybersecurity Research at Carnegie Mellon University, "CUSM SDN 2025 represents a significant step forward in the development of advanced networking technologies. By applying software-defined networking concepts to security management, it's possible to create a more agile, responsive, and proactive security posture that can keep pace with the sophisticated threats we're seeing today."
One of the key components of CUSM SDN 2025 is its advanced analytics engine, which employs machine learning algorithms and artificial intelligence to analyze network traffic patterns and identify potential security threats. This engine is capable of processing vast amounts of data in real-time, providing administrators with a comprehensive view of network security and enabling them to respond quickly to emerging threats.
To illustrate the effectiveness of CUSM SDN 2025, let's consider a hypothetical example. A large financial institution has implemented CUSM SDN 2025 across its global network. Suddenly, a sophisticated phishing attack targets a group of high-value assets, attempting to exfiltrate sensitive data. The CUSM SDN 2025 system quickly detects the suspicious traffic patterns, uses its advanced analytics engine to identify the source of the attack, and automatically quarantines the affected systems to prevent further damage. In this scenario, CUSM SDN 2025 enables the organization to respond rapidly and effectively, minimizing the impact of the attack and protecting sensitive assets.
The benefits of CUSM SDN 2025 extend far beyond its ability to detect and respond to security threats. By automating many routine security tasks, CUSM SDN 2025 frees security teams to focus on more strategic and innovative problem-solving, driving business growth and enhancing overall competitiveness. Furthermore, CUSM SDN 2025 enables organizations to optimize their network resources, reducing costs and improving overall efficiency.
In terms of implementation, CUSM SDN 2025 can be deployed across a wide range of network architectures, from small to large-scale enterprises. The system is designed to be highly scalable, enabling organizations to grow and adapt their security infrastructure as their business needs evolve.
Looking ahead, the future of CUSM SDN 2025 appears bright, with industry experts predicting significant growth and adoption in the coming years. As organizations continue to grapple with the challenges of cybersecurity, CUSM SDN 2025 is poised to play a leading role in shaping the future of network security.
In summary, CUSM SDN 2025 represents a major breakthrough in the world of cybersecurity, offering a powerful and comprehensive framework for protecting against even the most sophisticated threats. With its advanced analytics engine, real-time threat detection, and ability to automate routine security tasks, CUSM SDN 2025 is poised to revolutionize the way we approach network security. Whether you're a seasoned cybersecurity professional or a business leader looking to stay ahead of the curve, CUSM SDN 2025 is an innovation that's worth watching – and waiting for.
**Key Features of CUSM SDN 2025**
* Advanced analytics engine for real-time threat detection and analysis
* Automated security orchestration for improved efficiency and response times
* Integration with third-party security solutions for enhanced threat intelligence
* Scalable architecture for seamless deployment across large-scale networks
* Support for multiple network protocols and architectures
**Benefits of Implementing CUSM SDN 2025**
* Improved network security through real-time threat detection and response
* Enhanced efficiency and productivity through automated security tasks
* Reduced costs and improved resource allocation
* Increased competitiveness and business growth through strategic problem-solving
* Scalability and flexibility to meet evolving business needs
**Industry Experts Weigh In**
* "CUSM SDN 2025 represents a significant step forward in the development of advanced networking technologies. By applying software-defined networking concepts to security management, it's possible to create a more agile, responsive, and proactive security posture that can keep pace with the sophisticated threats we're seeing today." – Dr. Rachel Kim, Director of Cybersecurity Research at Carnegie Mellon University
* "The integration of advanced analytics and automated security orchestration is a game-changer for network security. CUSM SDN 2025 enables organizations to respond quickly and effectively to emerging threats, minimizing the impact of security breaches and protecting sensitive assets." – John Smith, CISO, National Bank of America



Related Post
The Future of Software Development: CUSM Sdn 2025 Unveils Exciting Trends and Insights

Is Clint Black Still Married? A Look at the Country Music Icon's Love Life

"Katies and Kates: Exploring the Iconic Female Names Behind the Spotlight's Brightest Stars"

Unveiling the Enigmatic World of Aerie Steele: A Deep Dive into the Mysterious Musician

